Is Bitcoin safe to use? It will be for you if you follow our tips for Bitcoin security and the safest ways to buy cryptocurrency.
Use a reputable exchange or app
Always buy and store bitcoin through well-established, regulated platforms. Look for platforms that are licensed, have a track record, and use standard security practices like two-factor authentication (2FA), encrypted communications, and cold storage for user funds.
Invity is a regulated European platform with a MiCA licence, making it one of the safest ways to buy bitcoin in the EU.
Enable two-factor authentication (2FA)
2FA adds an extra layer of security to your account. Even if someone gets your password, they’ll still need access to your second factor (usually your phone) to log in. Use an authenticator app (like Google Authenticator or Authy) rather than SMS-based 2FA, which can be vulnerable to SIM-swapping attacks.
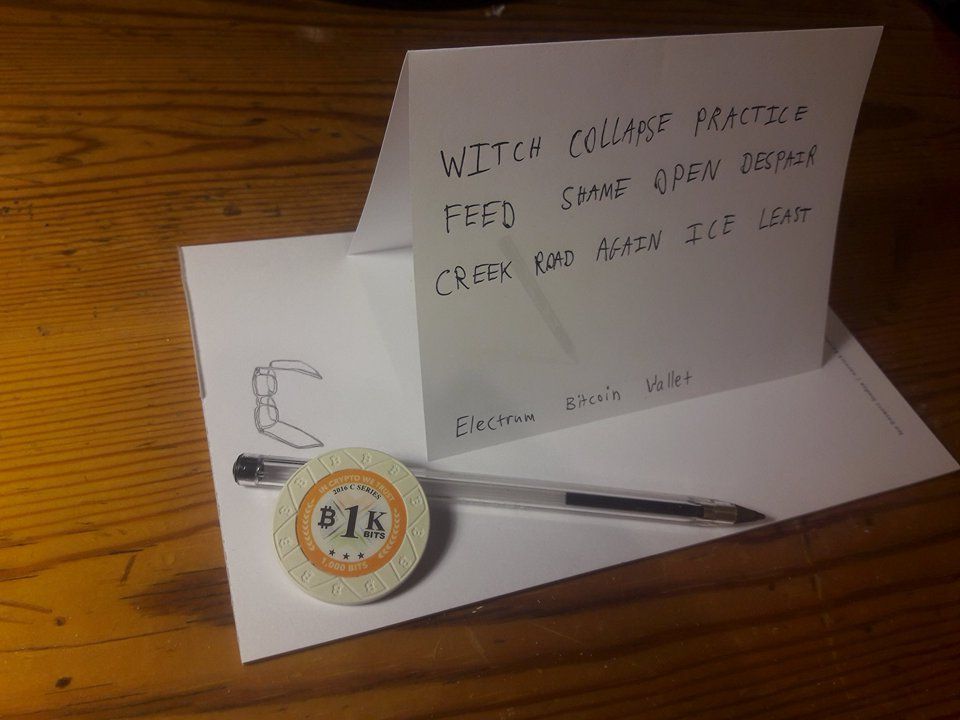
Use a hardware wallet for storage
Never leave large amounts of bitcoin on an exchange long-term. Exchanges can be hacked. A hardware wallet keeps your private keys offline and is the safest way to store significant amounts of bitcoin.
Be careful with public Wi-Fi
Avoid accessing your crypto accounts or making transactions on public Wi-Fi networks, which can be monitored. If you must use public Wi-Fi, use a VPN.
Recognize and avoid phishing
Phishing attacks try to trick you into giving up your login credentials or seed phrase. Always verify you’re on the correct website (check the URL carefully), never click suspicious links in emails or messages, and remember: no legitimate service will ever ask for your seed phrase or private key.
Use unique, strong passwords
Use a unique, randomly generated password for each crypto-related account. A password manager makes this easy to manage. Never reuse passwords across services.
Keep software updated
Keep your wallet software, device operating system, and antivirus software up to date. Many security vulnerabilities are patched through updates, and running outdated software is an unnecessary risk.