With crypto prices rising, scam attempts are too. Social media accounts, emails, websites, and more are hacked or just impersonated in clever ways—various forms of "phishing"—all in pursuit of stealing your personal information and eventually your digital money. The good news is that protecting yourself and your crypto investments doesn't have to be hard: by knowing what to look out for, using common sense, and trusting your instincts, you'll stay one step ahead of bad actors. That's why Invity is here to fill you in on some of the most common phishing scams and how to avoid them.
What is phishing?
Phishing is the most common type of cybercrime. When we think of crimes in the physical world, most of us can picture a masked man with a knife or gun using intimidation or violence to take what they want by force. This type of cybercrime, however, is based on deception and persuading victims to willingly hand over money or sensitive information like passwords. You may hear the term "social engineering" in the context of phishing scams—this describes how cybercriminals use psychological manipulation to get people to do what they want. This is where the term "phishing" comes from: convincing bait is used to lure and manipulate humans into bad situations just like you might use a worm to hook a fish in a lake or river.
Most phishing attempts boil down to this basic definition, but their real power comes through the many different channels that cybercriminals use. These can make their attacks appear unique and even trustworthy, or they may just catch the average person off guard.
What is social media phishing?
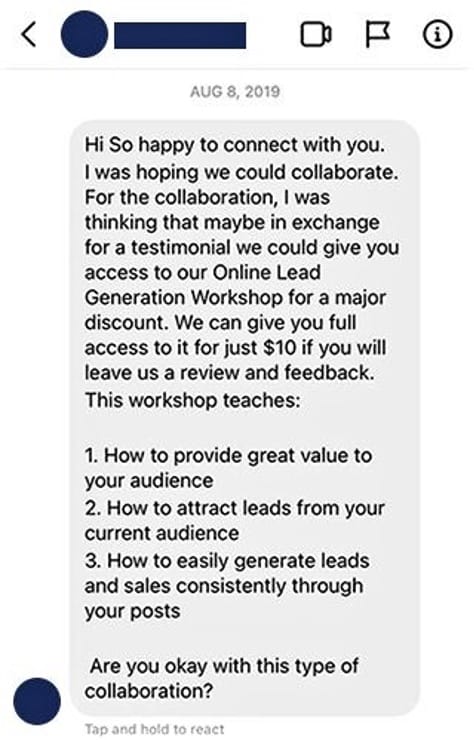
Social media is a part of almost everyone's daily life, and it is particularly prominent in the crypto space. Major, influential Bitcoin personalities rely heavily on their personal Twitter—ahem, X—accounts to share their opinions and interact with the community, and crypto businesses use places like LinkedIn to share product updates and attract new customers and partners. Unfortunately, with the billions of different accounts out there and often little to no way to verify who is suspicious and who isn't. The simplest social media phishing technique is sending private messages, or DMs. Some random account may message you, for instance, promising to provide you with a certain number of new followers for the low, low price of €5 dollars, payable via credit card. Once an aspiring influencer has provided their credit card info, the charge turns out to be many, many times larger.
However, scammers might instead ask that you send a certain amount of Bitcoin and request your wallet details to make the deal. They rely on people who aren't familiar with crypto to share their seed and/or their wallet's private key; these aren't only unnecessary for making Bitcoin transactions, they give bad actors full access to your crypto funds. If there is one thing to take away from this article, it's that you should never share your seed or private key with anyone.
How to avoid social media phishing
- Don't accept friend requests from people you don't know.
- Never share your seed, private key, or wallet app password with anyone.
What is spear phishing?
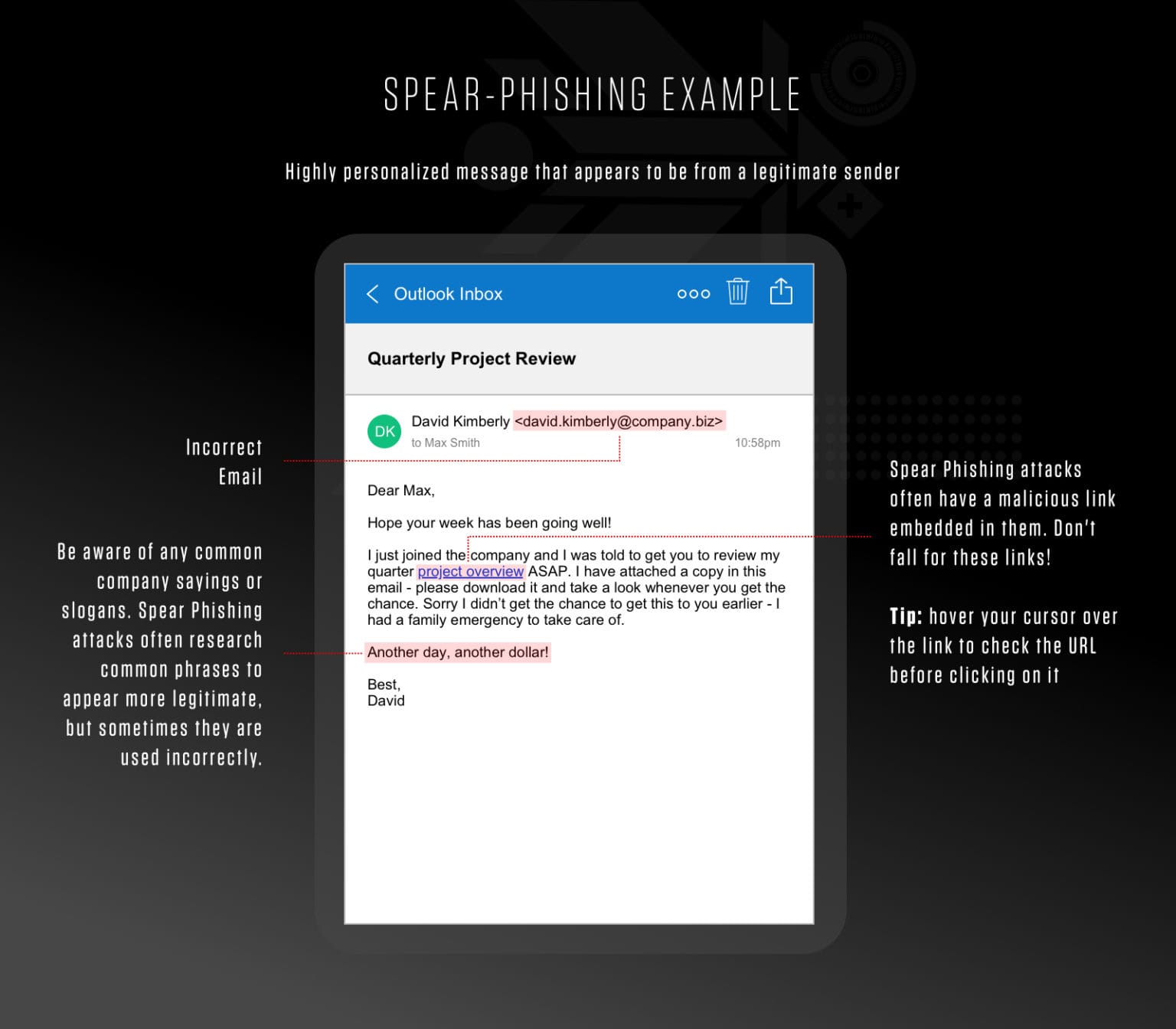
There are also more sophisticated attackers out there who personalize their attacks; when a phishing attempt is targeted to a specific individual or organization, it's called spear phishing. With surprisingly little technical know-how, it's easy for an attacker to set up an account or a full website that looks strikingly similar to a legitimate social media account, social media platform, bank, or utility company. Bad actors usually set up these sites based on large amounts of leaked data such as the names, account numbers, and email addresses of actual customers. Fraudsters then send emails customized, often using your real name and other details, usually with claims that your account has seen unauthorized activity.
How to avoid spear phishing
- Never blindly click on links requesting personal information.
- Carefully check the fine details. Fake email addresses and websites can be very similar to the real deal.
- Use unique login details for each site.
What is whaling?
Dedicated attackers may be able to refine their targeting even more in pursuit of "whales"—high-profile victims and bigger paydays. With patience and persistence, hackers frequently gain unauthorized access to businesses, receive payments, or introduce malware to large-scale targets.
How to avoid whaling
- Don't make yourself a target. Remember: it's good to talk about Bitcoin, just don't talk about your Bitcoin.
- Trust your gut. If something seems off or seems too good to be true, you're probably right.
What is smishing?
Smishing, or SMS phishing, usually uses similar techniques as large-scale phishing. As the name suggests, these cybercrime attempts come through text messages on your phone.
e

How to avoid smishing
- Don't respond to SMSs from unknown or suspicious numbers.
- Keep your phone's operating system up to date.
What is vishing?
Vishing is a mash-up too—"voice phishing"— and it too comes over the phone. In this scam, not only are you talking to a real person, giving you little time to think through the situation, but cybercriminals are also very talented at creating high-pressure situations.
How to avoid vishing
- Sign up to a do-not call list.
- Don't give in to a sense of urgency.
- Offer to call them back. Scammers often use "spoofing", routing calls through numbers that appear legitimate but they don't actually control.